
Cyber Security Problems You May Encounter When You Buy TikTok Followers
The digital world is not a safe place for anyone. Even if you spend a little money to buy a few hundred followers on TikTok, there are still cyber security threats that you should be aware of. Sure, boosting your follower count might seem like a great way to boost your popularity online and get more engagement with your content. So learning how to buy followers on TikTok safely is a must.
But if you don’t know what kind of security challenges are involved in the process and how to shield yourself against them, you could end up exposing yourself to malicious threats or scams without realizing it. So read on. You’re going to learn some security pitfalls associated with purchasing TikTok followers so that you can make an informed decision on whether or not this is a good idea for you.
Data Theft
 First of all, the most common problem that also has affected many Internet users is data theft. When you purchase TikTok followers, the third-party service provider has access to your personal information, such as your name, email address, and payment details. This means that if the company isn’t secure enough or doesn’t have a strict privacy policy, hackers could get their hands on this sensitive data and use it for identity theft or other malicious activities.
First of all, the most common problem that also has affected many Internet users is data theft. When you purchase TikTok followers, the third-party service provider has access to your personal information, such as your name, email address, and payment details. This means that if the company isn’t secure enough or doesn’t have a strict privacy policy, hackers could get their hands on this sensitive data and use it for identity theft or other malicious activities.
Malicious Ads & Links
Another thing you should be aware of is malicious ads and links that might appear on the pages of these third-party services. These could contain malware, ransomware, spyware, or any other dangerous software that could compromise your whole system as soon as you click on them. Make sure to always be vigilant and to only go through the official TikTok website if you’re looking to boost your followers.
Fake Followers
Your main goal is to grow your TikTok channel’s presence. So hoping you can get followers that are both active and real can make a huge impact on your goal. Unfortunately, some services sell fake followers – bots that are programmed to follow your account without actually engaging with it. There’s nothing wrong with having a few of these in your following, but it can easily get out of hand if you’re not careful. Make sure you read reviews before choosing a service, and make sure they offer real followers only.
All in all, buying followers on TikTok can be a risky endeavor. There are plenty of scammers out there who will take advantage of unsuspecting users and try to make a quick buck off them. So always be vigilant when browsing the web, and never give away your personal information without being absolutely sure that it’s going to a secure and reliable source. That way, you’ll be able to protect yourself from cyber security threats and make the most of your TikTok experience.…
Cyber Security Problems You May Encounter When You Buy TikTok Followers Read More


 The other reason that people use the VPN is that it preserves and respects their anonymity. You should note that a virtual private network allows you to explore the internet from a wide range of location servers. In this way, all traffic gets directed to and from the server. Also, your location and identity remain anonymous to the host website. Such anonymity helps you get protected from cyberattacks. That is because none can trace your internet activities.
The other reason that people use the VPN is that it preserves and respects their anonymity. You should note that a virtual private network allows you to explore the internet from a wide range of location servers. In this way, all traffic gets directed to and from the server. Also, your location and identity remain anonymous to the host website. Such anonymity helps you get protected from cyberattacks. That is because none can trace your internet activities.










 CO2 Extraction Process
CO2 Extraction Process
 Online fax can be defined as a virtual machine that can be used in sending and receiving faxes. The service gives you the fax number and users have the ability to receive and send faxes through the email, computer program, web interface, or a smartphone app. You do not need a phone line; you just need to have an internet connection.
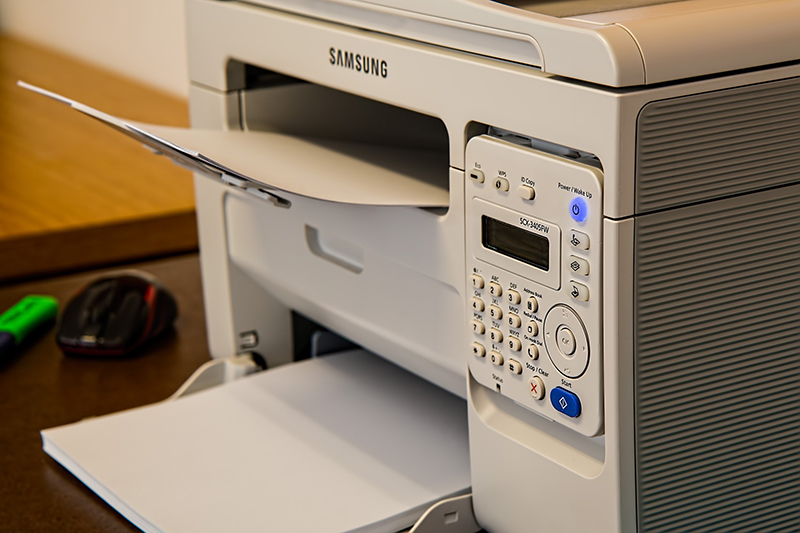
Online fax can be defined as a virtual machine that can be used in sending and receiving faxes. The service gives you the fax number and users have the ability to receive and send faxes through the email, computer program, web interface, or a smartphone app. You do not need a phone line; you just need to have an internet connection. In this case, fax software converts your machine to act as a fax machine. You need to have the right operating system. Currently, there is no fax modem for Apple computers. Most computers with Windows OS have Windows Fax and Scan. Linux has different software packages that support faxing. Fax software feels and acts like an email program. You need to download the document from Google Drive and then fax it through the software.
In this case, fax software converts your machine to act as a fax machine. You need to have the right operating system. Currently, there is no fax modem for Apple computers. Most computers with Windows OS have Windows Fax and Scan. Linux has different software packages that support faxing. Fax software feels and acts like an email program. You need to download the document from Google Drive and then fax it through the software.
 Ensure you have a legitimate online fax account. If you are yet to register, then you need to do so now. If you are sending only a few faxes, it is a good idea to use a free trial version. However, you should remember to cancel the subscription before the elapse of the trial period. This will ensure you are not billed.
Ensure you have a legitimate online fax account. If you are yet to register, then you need to do so now. If you are sending only a few faxes, it is a good idea to use a free trial version. However, you should remember to cancel the subscription before the elapse of the trial period. This will ensure you are not billed. After this, you will get an automatic confirmation from your Google fax services provider. Also, if the system was unable to send the fax, you will be notified as well. It is also possible to send the same document to several fax numbers at the same type. For instance, you can pull the numbers from an online spreadsheet instead of typing them in one-by-one.
After this, you will get an automatic confirmation from your Google fax services provider. Also, if the system was unable to send the fax, you will be notified as well. It is also possible to send the same document to several fax numbers at the same type. For instance, you can pull the numbers from an online spreadsheet instead of typing them in one-by-one.
 Nowadays there is much online software out there for you business owners, we can name a few, but exclusively for today, we’ll use Zoho for example. Zoho docs are famous for sharing documents for between company, and it is similar if not, the same as Microsoft Excel. This online software is perfect in case you want to share your work with a colleague without any problem at all.
Nowadays there is much online software out there for you business owners, we can name a few, but exclusively for today, we’ll use Zoho for example. Zoho docs are famous for sharing documents for between company, and it is similar if not, the same as Microsoft Excel. This online software is perfect in case you want to share your work with a colleague without any problem at all. If by any chance that your business has never changed for a long time, then it is a sign for you to start some changes in your business. And if you’re stuck in your sales, it is time to do something new.
If by any chance that your business has never changed for a long time, then it is a sign for you to start some changes in your business. And if you’re stuck in your sales, it is time to do something new.

 Keeping up with mobile-based applications can make entrepreneurs enjoy opportunities of giving customers the benefit of discount coupons. The benefits hitched to this is that customers will easily get attracted to the apps. They will also have the temptation of buying more with the aim of enjoying the benefits shortly. Mobile applications are considered effective measures in promoting businesses over the internet.
Keeping up with mobile-based applications can make entrepreneurs enjoy opportunities of giving customers the benefit of discount coupons. The benefits hitched to this is that customers will easily get attracted to the apps. They will also have the temptation of buying more with the aim of enjoying the benefits shortly. Mobile applications are considered effective measures in promoting businesses over the internet.

 Some businesses lack good disaster recovery plans since they are concerned about the costs. Disaster recovery and backup may be expensive if the methods you choose necessitate hardware purchase. For instance, if you need to back up all data in private servers, you have to invest in the same numbers of servers. Disaster recovery as a service is a solution that is provided by a third party. The software and hardware used are therefore owned by your service provider. The initial cost is thus small.
Some businesses lack good disaster recovery plans since they are concerned about the costs. Disaster recovery and backup may be expensive if the methods you choose necessitate hardware purchase. For instance, if you need to back up all data in private servers, you have to invest in the same numbers of servers. Disaster recovery as a service is a solution that is provided by a third party. The software and hardware used are therefore owned by your service provider. The initial cost is thus small.